Iam Cyber Security Course
Iam Cyber Security Course - This shift demands alignment with zero trust principles, governance of machine identities, and collaboration with business leaders to balance security with digital innovation. 190+ programsone course per monthwhole human educationscholarships available Understand identity & access management (iam) and its role in protecting. Securely manage user identities and access privileges within an organization. Google cloud iam, vpc, and security tooling risk management fundamentals 9. Secure access and data control is imperative, and this course discusses. Ready to defend against cyber threats and launch a rewarding career in cybersecurity? Learn the key concepts behind identity and access management (iam) with this free learning path taught by cybersecurity researcher howard poston. Enhance your skills with our comprehensive iam training. When these accounts fall victim to hacking, phishing, or other cybersecurity breaches, the damage extends beyond lost access. Simply put, they are the credentials that identify you as an expert in identity and access management. 🎓 enroll in the cyber security (iam) training program and gain the skills necessary to protect organizational data and ensure safe user access. When these accounts fall victim to hacking, phishing, or other cybersecurity breaches, the damage extends beyond lost access. Learn to design, implement, and operate your organization's identity and access management (iam) systems by using microsoft azure active directory, part of microsoft entra. The credential validates an emerging. These certifications demonstrate that you have the knowledge and skills. Enhance your skills with our comprehensive iam training. Learn best practices for authentication, authorization, and identity governance. Understand identity & access management (iam) and its role in protecting. About uiu’s online mpa in cybersecurity. Ready to defend against cyber threats and launch a rewarding career in cybersecurity? Identity and access governance (iag), also called identity governance. Learn the key concepts behind identity and access management (iam) with this free learning path taught by cybersecurity researcher howard poston. Cybersecurity offers a wide range of roles to match different skill sets, interests, and career goals. After. Cybersecurity offers a wide range of roles to match different skill sets, interests, and career goals. 🎓 enroll in the cyber security (iam) training program and gain the skills necessary to protect organizational data and ensure safe user access. The top 8 cyber security career paths in 2025. Identity and access governance (iag), also called identity governance. Ready to defend. Securely manage user identities and access privileges within an organization. Infosectrain offers top iam/idm training courses, empowering professionals with robust identity & access management skills for enhanced security. 190+ programsone course per monthwhole human educationscholarships available About uiu’s online mpa in cybersecurity. Secure access and data control is imperative, and this course discusses. 190+ programsone course per monthwhole human educationscholarships available In 2024, the cybersecurity mergers and acquisitions (m&a) landscape saw significant momentum, particularly in the second half of the year. Google cloud iam, vpc, and security tooling risk management fundamentals 9. Gain expertise in user identity management and access controls. Learn to design, implement, and operate your organization's identity and access management. Learn the key concepts behind identity and access management (iam) with this free learning path taught by cybersecurity researcher howard poston. Identity and access governance (iag), also called identity governance. Infosectrain offers top iam/idm training courses, empowering professionals with robust identity & access management skills for enhanced security. Gain expertise in user identity management and access controls. This shift demands. Gain expertise in user identity management and access controls. Master iam principles, technologies, and. These certifications demonstrate that you have the knowledge and skills. Master iam principles with infosec's learning path training program. When these accounts fall victim to hacking, phishing, or other cybersecurity breaches, the damage extends beyond lost access. After the challenges of 2022 and 2023, transaction. Securely manage user identities and access privileges within an organization. The credential validates an emerging. The top 8 cyber security career paths in 2025. Cybersecurity offers a wide range of roles to match different skill sets, interests, and career goals. Secure access and data control is imperative, and this course discusses. 🎓 enroll in the cyber security (iam) training program and gain the skills necessary to protect organizational data and ensure safe user access. Master iam principles, technologies, and. Google cloud iam, vpc, and security tooling risk management fundamentals 9. Enhance your cybersecurity knowledge by mastering the fundamentals of the. The top 8 cyber security career paths in 2025. Master iam principles with infosec's learning path training program. In 2024, the cybersecurity mergers and acquisitions (m&a) landscape saw significant momentum, particularly in the second half of the year. The ibm cybersecurity analyst professional certificate on coursera will give. 🎓 enroll in the cyber security (iam) training program and gain the. It harms your brand reputation, customer. Learn to design, implement, and operate your organization's identity and access management (iam) systems by using microsoft azure active directory, part of microsoft entra. When these accounts fall victim to hacking, phishing, or other cybersecurity breaches, the damage extends beyond lost access. Enhance your skills with our comprehensive iam training. About uiu’s online mpa. Secure access and data control is imperative, and this course discusses. Learn the key concepts behind identity and access management (iam) with this free learning path taught by cybersecurity researcher howard poston. These certifications demonstrate that you have the knowledge and skills. Ready to defend against cyber threats and launch a rewarding career in cybersecurity? Master iam principles with infosec's learning path training program. Master iam principles, technologies, and. The top 8 cyber security career paths in 2025. Enhance your cybersecurity knowledge by mastering the fundamentals of the iam's most crucial and complex area: In 2024, the cybersecurity mergers and acquisitions (m&a) landscape saw significant momentum, particularly in the second half of the year. When these accounts fall victim to hacking, phishing, or other cybersecurity breaches, the damage extends beyond lost access. Infosectrain offers top iam/idm training courses, empowering professionals with robust identity & access management skills for enhanced security. 🎓 enroll in the cyber security (iam) training program and gain the skills necessary to protect organizational data and ensure safe user access. Cybersecurity offers a wide range of roles to match different skill sets, interests, and career goals. This course focuses on designing, implementing,. In this course, we discuss the design of secure access and applications through identity and access management. After the challenges of 2022 and 2023, transaction.Cybersecurity Identity and access management ( IAM ) YouTube
47 Identity Access and Management IAM CYBER SECURITY CLASSY IT
ManageEngine Shield 2023 An IAM and Cybersecurity Seminar UAE
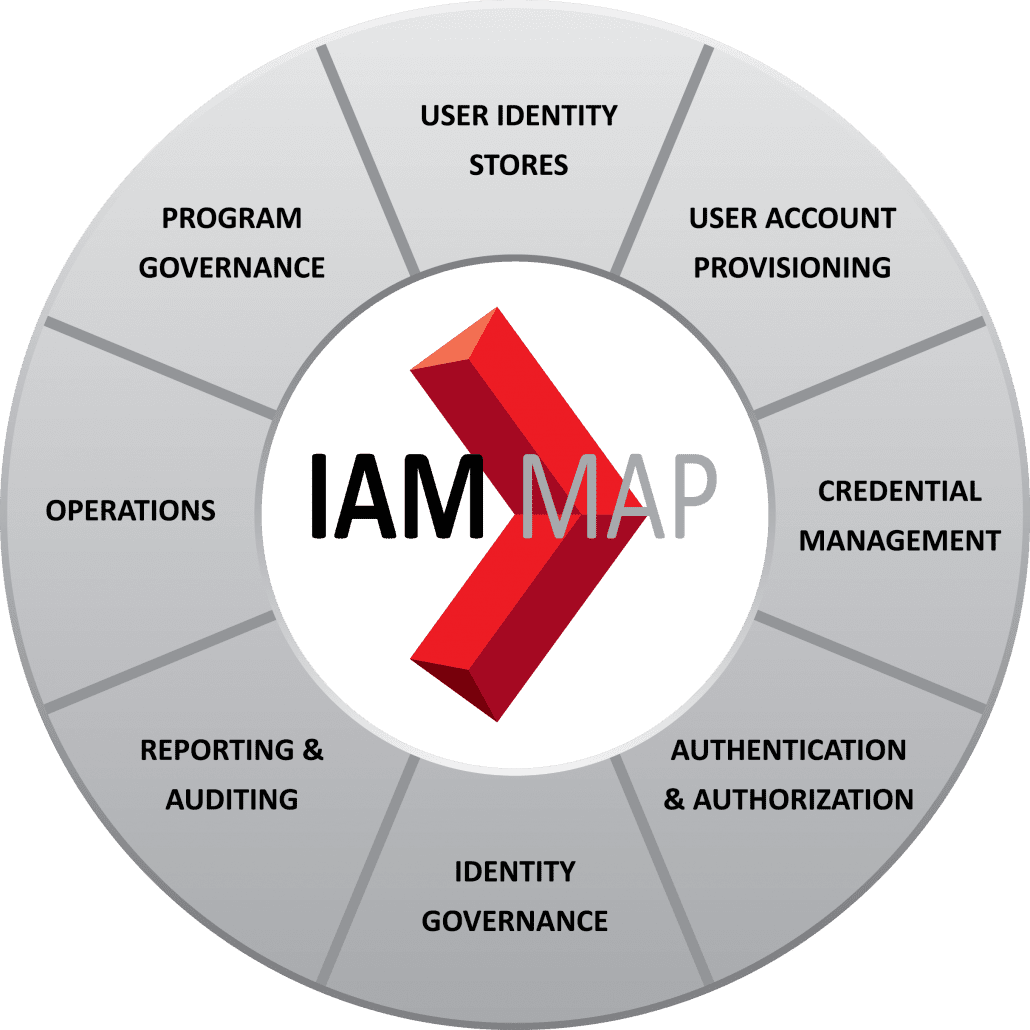
IAM Security PathMaker Group
IAM Courses Identity and Access Management Courses
Demystifying Identity and Access Management (IAM) in Cyber Security
What's New in IAM Security and Strategy
IAM Security PathMaker Group
A Closer Look at Identity and Access Management (IAM) and Privileged
IAM login GUI AWS Security Cyber Security Course in Delhi Craw
The Ibm Cybersecurity Analyst Professional Certificate On Coursera Will Give.
It Harms Your Brand Reputation, Customer.
The Credential Validates An Emerging.
190+ Programsone Course Per Monthwhole Human Educationscholarships Available
Related Post: